Introduction
In today’s digital-first environment, data leaks are no longer isolated technical failures. They are strategic risk events with long-term implications for organizations, individuals, and entire digital ecosystems. The growing attention around thejavasea.me leaks AIO-416 reflects increasing public awareness about how exposed data can create systemic vulnerabilities.
Search interest in thejavasea.me leaks AIO-416 shows that users are not only curious about what happened, but also concerned about the broader consequences. Data exposure affects privacy, operational stability, reputation, and governance standards.
This article provides a structured, in-depth analysis of thejavasea.me leaks AIO-416—explaining what it represents, how such incidents occur, who is affected, and what strategic lessons can be drawn for long-term digital resilience.
Understanding the Context Behind thejavasea.me Leaks AIO-416
To understand thejavasea.me leaks AIO-416, it is essential to examine how digital exposure events typically unfold. A data leak is rarely random. It is usually the result of accumulated weaknesses across systems, processes, and oversight structures.
Digital leaks often involve:
- Large volumes of stored records
- Misconfigured storage environments
- Compromised credentials
- Insecure data-sharing pipelines
- Insufficient governance oversight
When a repository or platform becomes associated with exposed datasets, it often signals structural vulnerabilities rather than a single technical error.
Thejavasea.me leaks AIO-416 appears to involve aggregated or categorized datasets. Aggregated exposures are particularly serious because the combined data increases correlation risks. When data points are connected, they can enable identity profiling, exploitation patterns, and reputational damage that extends beyond the initial breach.
From a strategic standpoint, aggregation multiplies impact. The risk is not only about what was exposed—but how that data can be analyzed, combined, and reused.
The Structural Anatomy of a Digital Leak Event
Understanding the lifecycle of exposure helps frame thejavasea.me leaks AIO-416 within a broader risk context. Most digital leak events follow structured phases.
Data Accumulation Phase
Data accumulates gradually through platform interactions, account creation, internal exports, third-party integrations, and automated systems.
At this stage, risk remains dormant. The system may function normally while silently expanding its exposure surface.
Vulnerability Introduction
Risk becomes active when weaknesses emerge, such as delayed security patches, poor access control configuration, weak encryption standards, or limited monitoring systems.
These issues are often incremental. Individually they may seem minor, but collectively they create structural instability.
Exposure or Breach
Exposure may occur through exploited vulnerabilities, compromised passwords, insider misuse, insecure APIs, or publicly accessible storage systems.
In many cases, the exposure remains undetected for an extended period, increasing the window of risk.
Amplification and Distribution
Once discovered, exposed datasets can spread rapidly through mirror repositories, indexing systems, or private distribution channels.
At this stage, containment becomes extremely difficult. The damage transitions from technical to reputational and strategic.
Thejavasea.me leaks AIO-416 fits within this broader structural model of digital exposure escalation.
Who Is Affected by thejavasea.me Leaks AIO-416?
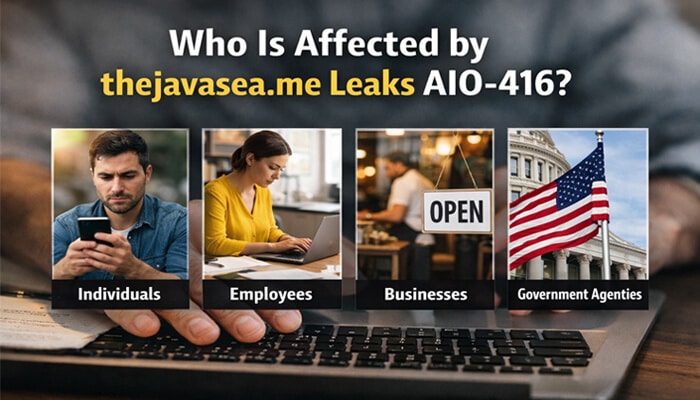
Data leaks rarely affect a single group. Their impact cascades across multiple layers.
Individuals
Individuals may experience identity profiling, credential reuse risks, social engineering attempts, and erosion of digital privacy. Even older data can be leveraged when aggregated.
The long-term consequences are often invisible at first but emerge gradually through targeted exploitation or reputation damage.
Organizations
Organizations may face regulatory scrutiny, operational disruption, reputational erosion, and legal exposure.
Beyond immediate remediation costs, trust loss is the most significant long-term impact. Stakeholders increasingly evaluate organizations based on their ability to safeguard data responsibly.
Digital Ecosystems
Modern digital environments are interconnected. One exposure can weaken confidence across partner networks, suppliers, cloud infrastructures, and integrated platforms.
Thejavasea.me leaks AIO-416 therefore represents not just a localized issue, but a signal of ecosystem-level vulnerability.
Common Misconceptions About Digital Leak Events
Misunderstandings often lead to inadequate responses. Several misconceptions deserve clarification.
“If the data is old, it is harmless.”
Historical data remains valuable when aggregated. Old credentials, behavioral patterns, or archived information can support profiling and exploitation strategies.
Age does not eliminate risk.
“Only large corporations are targeted.”
Smaller or mid-sized platforms are often targeted precisely because they may lack mature security infrastructure. Limited oversight increases vulnerability.
Scale does not guarantee safety.
“Technical fixes alone solve the problem.”
Security patches are necessary but insufficient. Sustainable protection requires governance reform, policy enforcement, cultural awareness, accountability systems, and continuous monitoring.
Data protection is a leadership issue—not only a technical one.
Strategic and Organizational Impact
When evaluating thejavasea.me leaks AIO-416 strategically, the question shifts from “what happened?” to “what does this reveal?”
Leak events often expose deeper systemic weaknesses:
- Over-centralization of data
- Inadequate data minimization practices
- Weak encryption governance
- Fragmented oversight structures
- Insufficient audit transparency
Organizations that treat data purely as an asset overlook its liability dimension. Every stored record increases exposure risk.
Executives increasingly recognize that cybersecurity maturity must be embedded into organizational strategy. Board-level oversight is becoming standard in resilient institutions.
Failure to adopt structured governance can lead to long-term trust erosion, stakeholder disengagement, and competitive disadvantage.
Risk Mitigation Framework: A Structured Approach
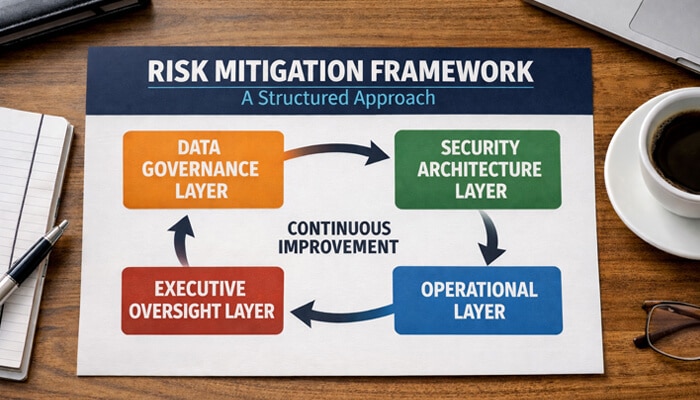
To reduce the probability and impact of events similar to thejavasea.me leaks AIO-416, organizations should implement layered protection strategies.
Data Governance Layer
This includes clear ownership assignment, strict access tier classification, data minimization policies, and encryption standards for both storage and transmission.
Security Architecture Layer
Zero-trust access models, continuous vulnerability scanning, multi-factor authentication enforcement, and real-time anomaly detection reduce unauthorized exposure.
Operational Layer
Incident response plans, simulation exercises, employee awareness programs, and third-party audits strengthen operational resilience.
Executive Oversight Layer
Leadership involvement ensures accountability. Regular cyber-risk assessments, transparent reporting systems, and independent testing create structured oversight.
Security becomes sustainable only when embedded across organizational layers.
Long-Term Digital Transformation Lessons
Thejavasea.me leaks AIO-416 reinforces critical transformation priorities for modern institutions.
Data must be treated as both an asset and a liability. Aggregation increases analytical value but also amplifies exposure risk.
Security maturity cannot remain static. Threat landscapes evolve continuously, requiring adaptive governance.
Transparency strengthens resilience. Institutions that communicate responsibly during incidents often preserve long-term trust more effectively than those that delay disclosure.
Most importantly, prevention is significantly less costly than remediation. Strategic investment in security infrastructure yields measurable long-term returns.
Authority and Trust: Why This Issue Matters in Modern Contexts
Data exposure incidents have evolved into trust crises. In digital economies, trust functions as strategic capital.
The implications of thejavasea.me leaks AIO-416 extend beyond technical failure. They underscore the necessity of ethical data stewardship and responsible governance frameworks.
Investors, regulators, and consumers increasingly evaluate organizations based on digital integrity standards. Governance maturity is emerging as a competitive differentiator.
Ethical data practices—including consent clarity, minimization principles, and accountability transparency—contribute directly to long-term sustainability.
Institutions that integrate ethical frameworks into technical design demonstrate stronger resilience in volatile digital environments.
Frequently Asked Questions
What is thejavasea.me leaks AIO-416?
Thejavasea.me leaks AIO-416 refers to a data exposure event involving aggregated digital datasets associated with a repository or indexing system. It represents a broader discussion about digital security risks and governance vulnerabilities in modern platforms.
Why is thejavasea.me leaks AIO-416 considered significant?
Its significance lies in the aggregation factor. When multiple datasets are combined, correlation risks increase, amplifying privacy exposure, exploitation potential, and reputational consequences for affected parties.
Who is most impacted by thejavasea.me leaks AIO-416?
Individuals whose data was exposed, organizations connected to the datasets, and broader digital ecosystems may all be impacted. The severity depends on the type, sensitivity, and scope of the exposed information.
Can events like thejavasea.me leaks AIO-416 be prevented?
While no system is immune, layered security architecture, strong governance frameworks, continuous monitoring, and executive oversight significantly reduce the likelihood and impact of such exposure events.
Does older data reduce the risk in thejavasea.me leaks AIO-416?
Older data still holds value when aggregated. Historical information can support profiling, credential validation, and social engineering attempts. Age does not eliminate exposure risk.
Conclusion
The discussion around thejavasea.me leaks AIO-416 highlights a broader transformation in how digital exposure events must be understood. They are not isolated technical mishaps but strategic risk indicators that reveal structural weaknesses in governance, architecture, and oversight.
Organizations that treat such events as minor IT disruptions overlook the deeper lesson. Sustainable digital resilience requires integrated security systems, ethical stewardship, executive accountability, and continuous improvement.
In an era where digital trust defines competitive advantage, proactive security maturity is foundational. The critical question is not whether exposure risks exist—but whether institutions are prepared to manage them strategically, responsibly, and sustainably.